What Is Azure Bastion And How To Allow Azure Bastion On A VM
Should you handle a distant server or digital machine, I’m certain you might be accustomed to RDP and SSH. RDP and SSH, each are used to remotely entry digital machines and servers. RDP and SSH are additionally used to entry digital machines in a cloud reminiscent of Azure and AWS.
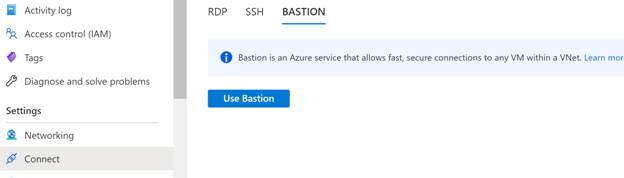
Whenever you login to your Azure account, click on on Join within the Settings, you will notice 3 ways to hook up with your digital machine, RDP, SSH, and BASTION. See under. On this article, let’s study what’s Azure Bastion and when and why it is best to use Azure Bastion to hook up with your Azure digital machine.
Azure Bastion
Digital Non-public Networks (VPNs) are used to supply a safe connectivity to a distant server or distant VM from a consumer machines, however most VPNs require you to put in a VPN consumer utility on a machine. VPN makes use of a public IP on a distant machine to hook up with the machine.
Azure Bastion is a PaaS service of Azure that enables you connect with an Azure digital machine utilizing your browser and gives safe and seamless RDP/SSH connectivity instantly from the Azure portal over TLS. In a typical RDP connection, a digital machine must configure a public IP that’s uncovered to the world and a consumer machine makes use of that IP and login credentials to attach and login to the digital machine. Whenever you join by way of Azure Bastion, your digital machines don’t want a public IP handle, agent, or particular consumer software program.
Bastion gives safe RDP and SSH connectivity to the entire VMs within the digital community during which it’s provisioned. Utilizing Azure Bastion protects your digital machines from exposing RDP/SSH ports to the skin world, whereas nonetheless offering safe entry utilizing RDP/SSH.
Function of Digital Non-public Community (VPN) in distant connectivity
A Digital Non-public Community or VPN permits a consumer gadget to hook up with a distant server or machine by way of a non-public community, The non-public community ensures that the info transferred over the community is encrypted and a 3rd celebration will likely be unable to decrypt it. A VPN additionally ensures that folks linked to the distant machine are authenticated and the info despatched over the community is tough to alter and if information is tempered, it may be detected.
A number of corporations present VPN purchasers as their service. Most of those corporations are IT safety corporations.
A few of the widespread enterprise VPNs are Cisco AnyConnect, FortiClient by Fortinet, GlobalProtect by Palo Alto Networks, CloudVPN by Google, Citrix Gateway, SonicWall World VPN Consumer, Zscaler Non-public Entry, Enterprise Software Entry by Akamai, IKEv2 by Apple, and plenty of extra. There are additionally some common VPNs for people reminiscent of ExpressVPN, NordVPN, and IPVanish.
RDP vs SSH vs Bastian
RDP (Distant Desktop Protocol) is a Home windows protocol that’s used to entry distant Home windows digital machines and Home windows servers. RDP requires a port to be opened on the distant machine, VM or bodily server. As a result of RDP ports are sometimes opened to the Web and obtainable publicly, they’re typically attacked by the hackers and bots. To guard RDP situations, corporations typically use a digital non-public community (VPN) and a type of multi issue authentication (MFA).
Be aware
For safety causes, it’s extremely beneficial to not use RDP with out VPN connections. Additionally, be certain RDP periods should not energetic if you find yourself performed by manually logging off RDP periods.
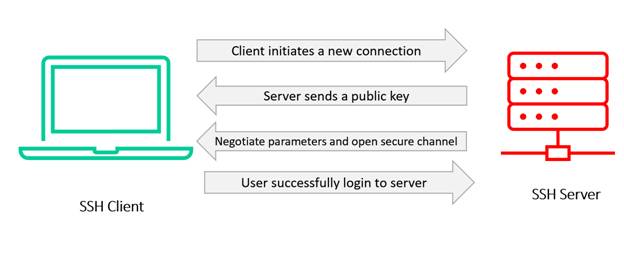
SSH (Safe Shell) protocol much like RDP permits a consumer machine to speak to a different machine (server) and switch information. The benefit of SSH is it protects the communications safety and integrity with robust encryption.
SSH protocol is utilized in company networks for,
- Offering safe entry for customers and automatic processes
- Interactive and automatic file transfers
- Issuing distant instructions
- Managing community infrastructure and different mission-critical system elements.
The next diagram reveals SSH communication between a consumer and a server (two computer systems).
Azure Bastion is a brand new totally platform-managed PaaS service you provision inside your digital community. It gives safe and seamless RDP/SSH connectivity to your VMs instantly within the Azure portal over SSL. Whenever you join by way of Azure Bastion, your digital machines don’t want a public IP handle.
Why use Azure Bastion?
Azure Bastion makes distant connection safer by creating a non-public digital community that’s safer and restricts entry to take away machines and therefore limits threats reminiscent of port scanning and different kinds of malware concentrating on your VMs
How does Azure Bastion work?
Watch Microsoft’s Ashish Jain and Scott Hanselman to indicate how Azure Bastion provides you safe and seamless RDP and SSH entry to your digital machines. Now you’ll be able to securely entry your VMs over SSL from the Azure portal and with out exposing public IP addresses.
Azure Bastion Structure
Right here is how Azure Bastion works in accordance with Azure docs.
Azure Bastion deployment is per digital community, not per subscription/account or digital machine. When you provision an Azure Bastion service in your digital community, the RDP/SSH expertise is offered to all of your VMs in the identical digital community.
RDP and SSH are among the elementary means by means of which you’ll be able to connect with your workloads working in Azure. Exposing RDP/SSH ports over the Web is not desired and is seen as a big menace floor. That is typically resulting from protocol vulnerabilities. To include this menace floor, you’ll be able to deploy bastion hosts (also referred to as jump-servers) on the public facet of your perimeter community. Bastion host servers are designed and configured to face up to assaults. Bastion servers additionally present RDP and SSH connectivity to the workloads sitting behind the bastion, in addition to additional contained in the community.
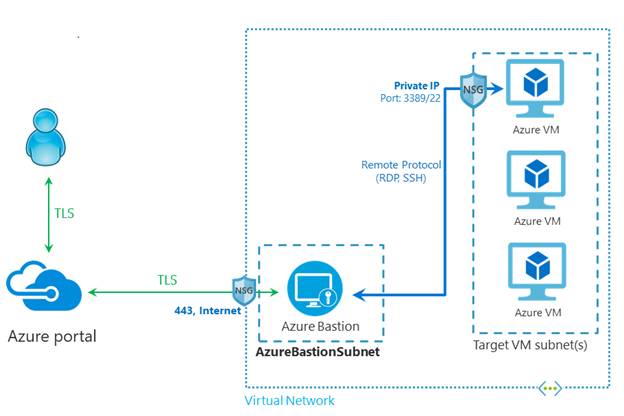
This determine reveals the structure of an Azure Bastion deployment. On this diagram,
The Bastion host is deployed within the digital community.
The consumer connects to the Azure portal utilizing any HTML5 browser.
The consumer selects the digital machine to hook up with.
With a single click on, the RDP/SSH session opens within the browser.
No public IP is required on the Azure VM.
Key options of Azure Bastion
The next options can be found,
RDP and SSH instantly in Azure portal: You possibly can instantly get to the RDP and SSH session instantly within the Azure portal utilizing a single click on seamless expertise.
Distant Session over TLS and firewall traversal for RDP/SSH: Azure Bastion makes use of an HTML5 primarily based internet consumer that’s mechanically streamed to your native gadget, so that you just get your RDP/SSH session over TLS on port 443 enabling you to traverse company firewalls securely.
No Public IP required on the Azure VM: Azure Bastion opens the RDP/SSH connection to your Azure digital machine utilizing non-public IP in your VM. You do not want a public IP in your digital machine.
No problem of managing NSGs: Azure Bastion is a completely managed platform PaaS service from Azure that’s hardened internally to supply you safe RDP/SSH connectivity.
You need not apply any NSGs on Azure Bastion subnet. As a result of Azure Bastion connects to your digital machines over non-public IP, you’ll be able to configure your NSGs to permit RDP/SSH from Azure Bastion solely. This removes the effort of managing NSGs every time it’s worthwhile to securely connect with your digital machines.
Safety towards port scanning: As a result of you do not want to reveal your digital machines to public Web, your VMs are protected towards port scanning by rogue and malicious customers situated exterior your digital community.
Shield towards zero-day exploits. Hardening in a single place solely: Azure Bastion is a completely platform-managed PaaS service. As a result of it sits on the perimeter of your digital community, you don’t want to fret about hardening every of the digital machines in your digital community. The Azure platform protects towards zero-day exploits by conserving the Azure Bastion hardened and all the time updated for you.
Allow Azure Bastion on a VM in Azure
Comply with these steps to allow Azure Bastian on a VM out of your Azure Portal.
First, we’ll create bastion host. That is required to create a safe connection to a VM within the VNet.
Create a bastion host
- From the Residenceweb page, choose VM on which you wish to allow bastion.
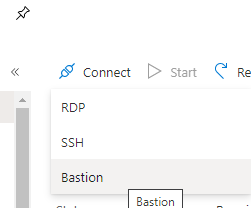
- Click on Join and choose Bastion
- Choose Create.
- On the Create a Bastionweb page, configure a brand new Bastion useful resource.
Fill the next info on this web page
Subscription
The Azure subscription you wish to use to create a brand new Bastion useful resource.
Useful resource Group
The Azure useful resource group during which the brand new Bastion useful resource will likely be created. If you do not have an present useful resource group, you’ll be able to create a brand new one.
Title
The identify of the brand new Bastion useful resource.
Area
The Azure public area that the useful resource will likely be created in.
Digital community
The digital community during which the Bastion useful resource will likely be created. You possibly can create a brand new digital community within the portal throughout this course of, or use an present digital community. In case you are utilizing an present digital community, be certain the present digital community has sufficient free handle house to accommodate the Bastion subnet necessities. Should you do not see your digital community from the dropdown, be sure you have chosen the proper Useful resource Group.
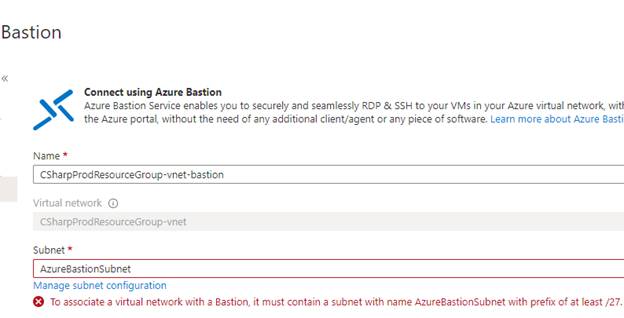
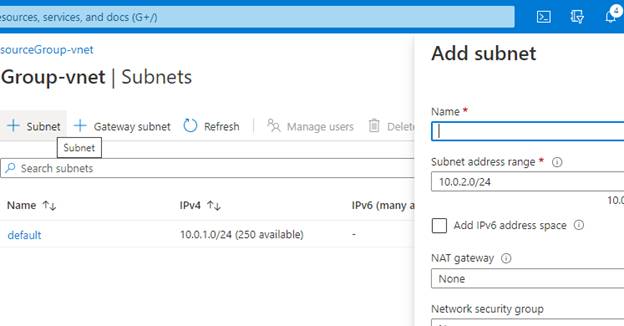
Subnet
When you create or choose a digital community, the subnet subject will seem. The subnet in your digital community is the place the brand new Bastion host will likely be deployed. The subnet will likely be devoted to the Bastion host. Choose Handle subnet configuration and create the Azure Bastion subnet. Choose +Subnet and create a subnet utilizing the next pointers,
- The subnet have to be named AzureBastionSubnet.
- The subnet have to be at the least /27 or bigger.
You need not fill out further fields. Choose OK after which, on the high of the web page, choose Create a Bastion to return to the Bastion configuration web page.
Public IP handle
The general public IP of the Bastion useful resource on which RDP/SSH will likely be accessed (over port 443). Create a brand new public IP. The general public IP handle have to be in the identical area because the Bastion useful resource you might be creating. That is IP handle doesn’t have something to do with any of the VMs that you just wish to connect with. It is the general public IP for the Bastion host useful resource.
Public IP handle identify
The identify of the general public IP handle useful resource. You possibly can go away the default.
Public IP handle SKU
This setting is prepopulated by default to Normal. Azure Bastion makes use of/helps solely the Normal Public IP SKU.
Task
This setting is prepopulated by default to Static.
After filling all the data, choose Create.
It should take three to four min to configure Bastion host.
When you’ve got configured the JIT then take away that earlier than connecting by means of bastion.
Hook up with a VM
Navigate to a VM tat you wish to connect with, Choose Join and choose Bastion from the drop down.
Choose use bastion
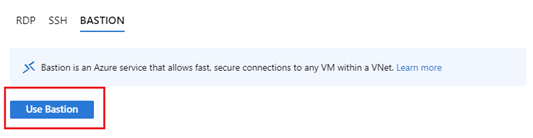
Enter the Username and Password after which click on on join.
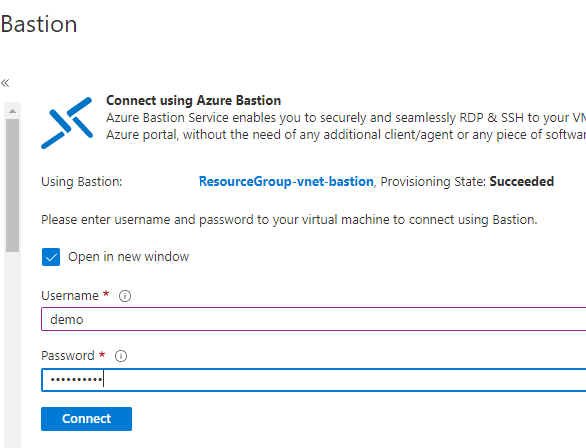
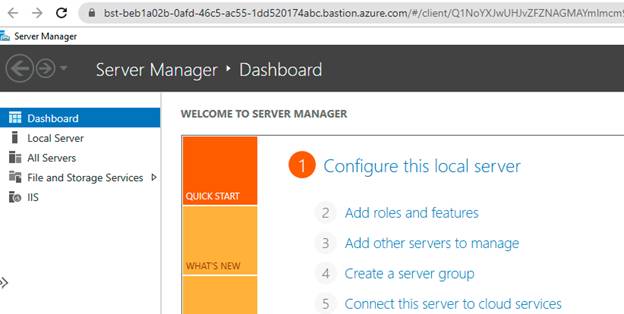
The RDP connection to this digital machine by way of Bastion will open instantly within the Azure portal (over HTML5) utilizing port 443 and the Bastion service.
We additionally want so as to add some inbound and outbound rule to Community Safety Group for higher communication. Azure Bastion is deployed particularly to AzureBastionSubnet.
Ingress Site visitors
For management airplane connectivity, we’ll allow port 443 inbound from GatewayManager service tag. This permits the Gateway Supervisor to have the ability to discuss to Azure Bastion.
For information airplane communication between the underlying elements of Azure Bastion, allow ports 8080, 5701 inbound from the VirtualNetwork service tag to the VirtualNetwork service tag. This permits the elements of Azure Bastion to speak to one another.

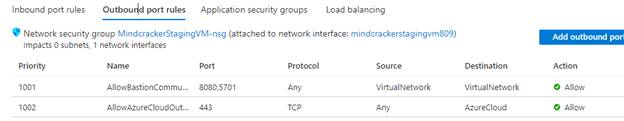
Egress Site visitors
For information airplane communication between the underlying elements of Azure Bastion, allow ports 8080, 5701 outbound from the VirtualNetwork service tag to the VirtualNetwork service tag. This permits the elements of Azure Bastion to speak to one another.
Azure Bastion wants to have the ability to join to numerous public endpoints inside Azure (for instance, for storing diagnostics logs and metering logs). Because of this, Azure Bastion wants outbound to 443 to AzureCloud service tag.
References
https://docs.microsoft.com/en-us/azure/bastion/bastion-overview