Set up Terraform On Home windows And Authenticate Terraform To Azure
Overview
Utilizing instruments for infrastructure as code (IaC), you may management infrastructure with no graphical consumer interface through the use of configuration information. IaC lets you outline useful resource configurations which you can model, reuse, and share, permitting you to develop, modify, and handle your infrastructure in a safe, reliable, and repeatable method.
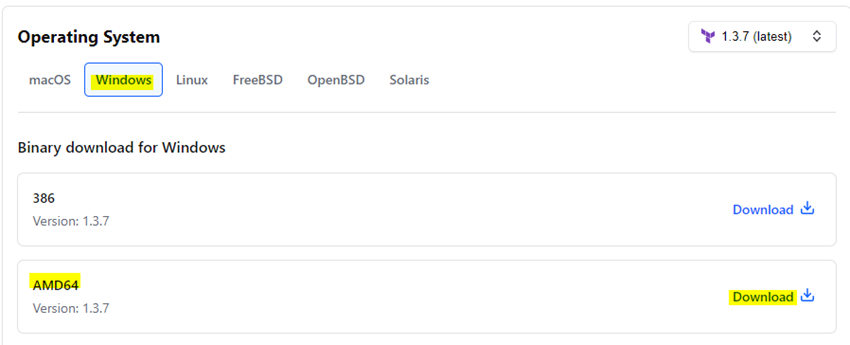
Set up Terraform for Home windows
Obtain Terraform. Choose Home windows Tab and Obtain AMD 64.
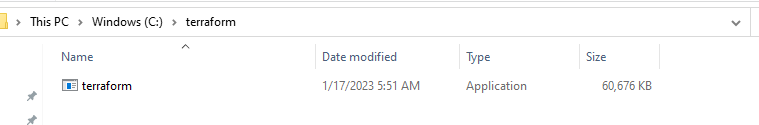
From the obtain, extract the executable to a listing of your alternative (for instance, c:terraform).
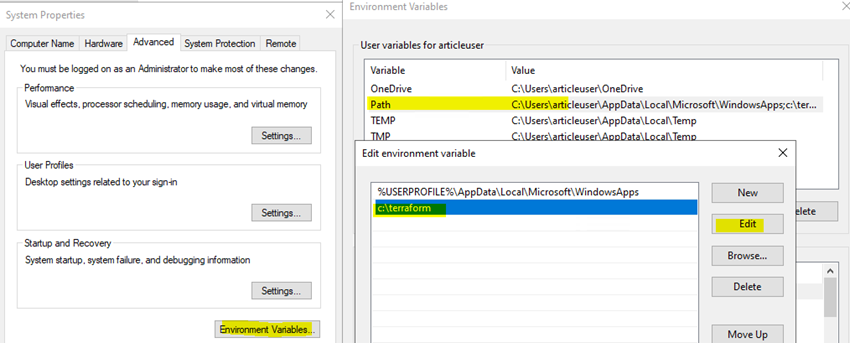
Replace your system’s world path to the executable.
The trail is within the registry however normally you edit via this interface:
- Go to Management Panel -> System -> System settings -> Setting Variables.
- Scroll down in system variables till you discover PATH.
- Click on edit and alter accordingly.
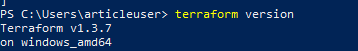
Open energy Shell Run as Admin and Confirm the worldwide path configuration with the ‘terraform’ command.
terraform -version
Set up the Azure CLI software
You’ll use the Azure CLI software to authenticate with Azure.
Set up the Azure CLI software – Open Energy shell as Run as Admin and run this,
Invoke-WebRequest -Uri https://aka.ms/installazurecliwindows -OutFile .AzureCLI.msi; Begin-Course of msiexec.exe -Wait -ArgumentList ‘/I AzureCLI.msi /quiet’; rm .AzureCLI.msi
Authenticate utilizing the Azure CLI
Terraform should authenticate to Azure to create infrastructure.
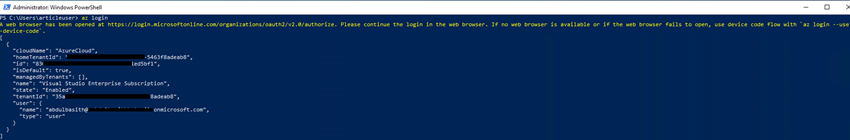
Open PowerShell as run as admin and Run az login with none parameters and observe the directions to sign up to Azure.
az login
Upon profitable sign-in, az login shows an inventory of the Azure subscriptions related to the logged-in Microsoft account, together with the default subscription.
To substantiate the present Azure subscription, run-
az account present
To make use of a selected Azure subscription, run az account set.
az account set –subscription “<subscription_id_or_subscription_name>”

Create a Service Principal
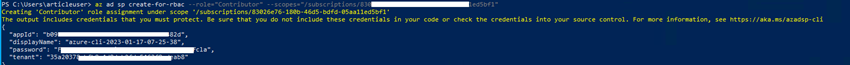
Make a Service Principal subsequent. A service principal is an Azure Lively Listing utility that has the authentication tokens required by Terraform to behave in your behalf. The subscription ID you gave within the previous step needs to be added to the SUBSCRIPTION ID>.
az advert sp create-for-rbac –role=”Contributor” –scopes=”/subscriptions/<SUBSCRIPTION_ID>”
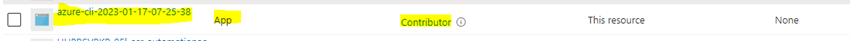
Navigate to Azure portal – Subscription – IAM – Position Assignments, Then you may see the App – Contributor
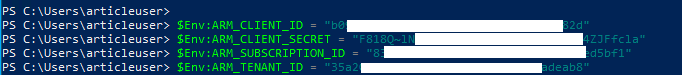
Set your surroundings variables
As a substitute of storing these values in your Terraform setup, HashiCorp advises defining them as surroundings variables.
In your Powershell terminal, set the next surroundings variables. You should definitely replace the variable values with the values Azure returned within the earlier command.
$Env:ARM_CLIENT_ID = "<APPID_VALUE>"
$Env:ARM_CLIENT_SECRET = "<PASSWORD_VALUE>"
$Env:ARM_SUBSCRIPTION_ID = "<SUBSCRIPTION_ID>"
$Env:ARM_TENANT_ID = "<TENANT_VALUE>"
That’s all. I’ll meet with my subsequent weblog, write configurations, and construct infrastructure—Terraform Azure Instance (Useful resource Group, Digital Community, and Digital Machine)
Abstract
We realized the way to Set up Terraform on Home windows and Authenticate Terraform to Azure. Please go away a remark within the remark field in case you have any questions.