How To Setup Digital Community Integration On Azure Knowledge Lake Storage
Introduction
On this article, we are going to learn to apply networking management via Digital community integration to the Azure Knowledge Lake Storage created from the final article.
By establishing Digital community integration, we enable companies on the Digital community and subnet to attach and entry the information lake with out including an IP exception to the firewall. It is very important word that the connection between the information lake and the Digital community is thru the general public endpoint and IP deal with.
Challenges
Within the final article, we created our knowledge lake storage with firewall enabled. To handle and configure the information lake, we had so as to add the admin IP addresses to the firewall exceptions. It is a safety concern as many people are working from house and our IP addresses can change. Moreover, we have to present a method for Knowledge Engineers and Knowledge Scientists to entry the information lake. We have to present an answer with out modifying the firewall exception listing.
We are able to obtain this by implementing Digital community integration with our knowledge lake. To maintain issues easy, we are going to use Digital Machines (VMs) supplied by our infrastructure crew in Azure to entry and handle our knowledge lake.
Tutorial
Earlier than we dive into the tutorial, let’s recap on what we have now achieved within the final article:
- Created Azure Knowledge lake Storage via the Azure Portal.
- Enabled infrastructure encryption, encryption-at-rest, and TLS 1.2.
- An enabled Firewall permits trusted Azure companies to entry the information lake.
- Enabled Comfortable delete for containers and blobs.
- Disabled Blob public entry.
- Created customized tags for value monitoring.
Digital community integration
-
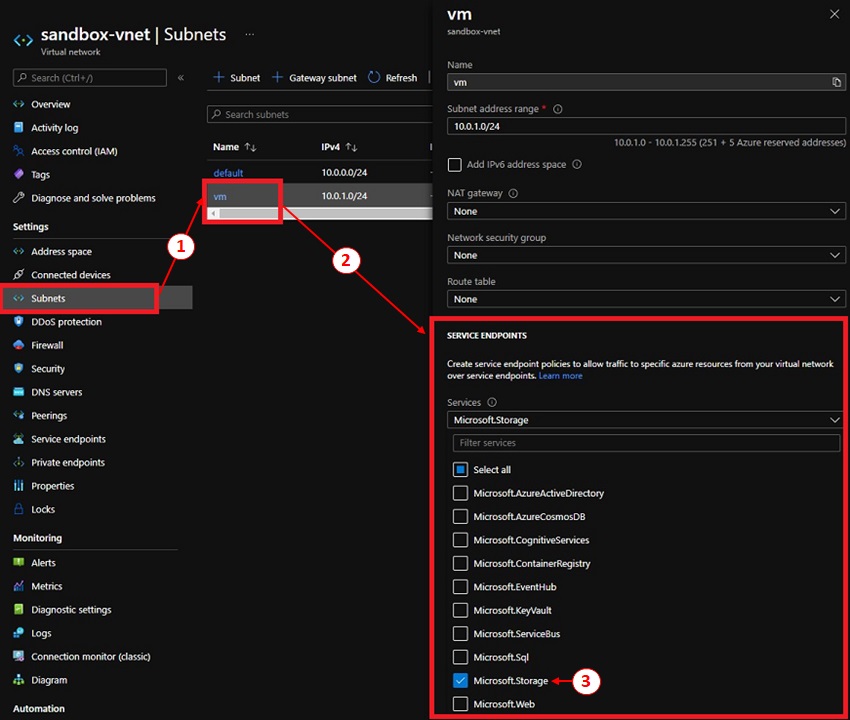
The infrastructure crew has provisioned the Knowledge platform admin crew with digital machines to help Cloud companies. They’re created on the identical subnet inside the Digital Community (VNet). We have to make sure the subnet has ‘Microsoft.Storage’ service endpoints enabled,
- Choose the Digital community and the Subnet ‘vm’. This may convey up a sub-panel with the subnet info.
- Underneath Service Endpoints, click on on the ‘Providers’ dropdown to develop the listing.
- Allow ‘Microsoft.Storage’ is just not checked and click on ‘Save’.
-
Wait till the notification confirms the Service Endpoint is added earlier than continuing to the subsequent step.
-
Now we will add the Digital Community and Subnet to our knowledge lake,
- Navigate to our knowledge lake, underneath ‘Safety & networking’, choose ‘Networking’.
- Underneath the ‘Firewalls and digital networks’ tab, underneath ‘Digital networks’, click on on ‘+ Add present digital community’. This may convey up the ‘Add networks’ aspect panel.
- Choose the Digital Community and Subnet the place the Digital machines are created (with service endpoint enabled), then click on ‘Okay’ to substantiate the choice,
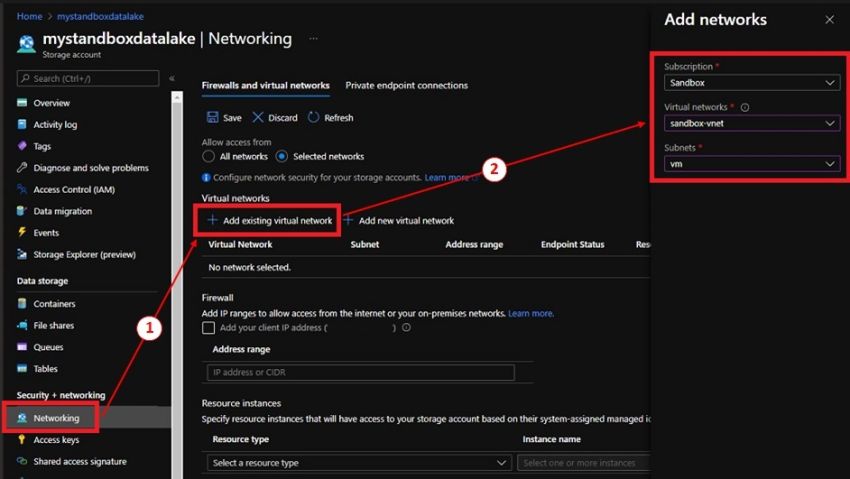
- To finalize our settings, click on ‘Save’ underneath the ‘Firewalls and digital networks’ tab.
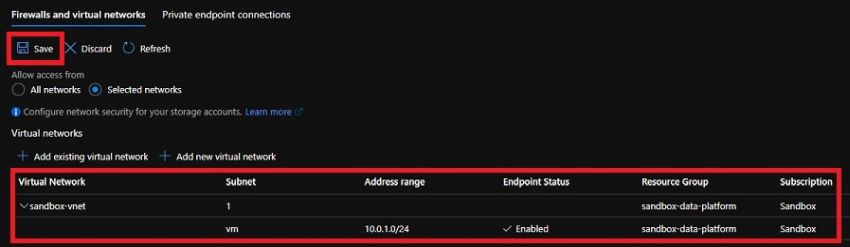
-
Now, we will login to our VM to confirm our settings are working,
- Login to the Azure portal and navigate to our knowledge lake.
- Click on on the ‘Storage Explorer (preview) menu merchandise. This may open the Cloud Storage Explorer.
- Expend the containers to make sure you don’t get an error. In my case, I created some containers to point out it opens up appropriately.
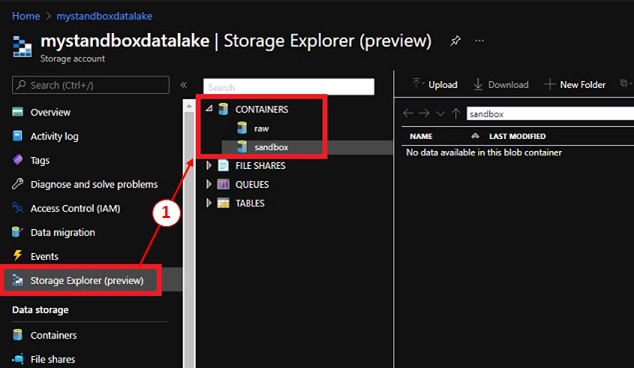
-
Lastly, we will repeat the steps within the tutorial so as to add a number of Digital networks and Subnets to our knowledge lake.
References
Abstract
On this tutorial, we enhanced our safety by eradicating the necessity of updating the firewall guidelines as our IP modifications. We achieved this by implementing Digital community integration with the digital machines in Azure.
Completely happy Studying!