Azure DevOps – Entry Restriction Of Azure App Service Utilizing Azure Administration Portal
This text is split into three elements,
- Azure DevOps
Entry Restriction of Azure App Service utilizing Azure Administration Portal – We’ll discover ways to limit entry to the Azure App Service manually utilizing the Azure Portal. - Azure DevOps
Bulk IP Handle Restriction of Azure App Service dynamically utilizing PowerShell– We discover ways to leverage PowerShell scripting to dynamically do bulk insertion of IP Addresses for configuring entry restrictions for the Azure App Service. - Azure DevOps
Automate Bulk IP Handle Restriction of Azure App Service dynamically utilizing PowerShell & Azure DevOps Pipeline We’ll discover ways to automate the method of Entry Restriction each time there’s a change within the checklist of IP addresses utilizing Azure DevOps Pipelines.
Conditions
- Azure Subscription
- Azure App Service
Introduction
Azure App Service is a PaaS providing from Microsoft Azure the place we will host net purposes. As soon as the net purposes are deployed anybody can entry the app over the web.
Under are some eventualities the place you may wish to limit the entry of the App Service,
- Your utility is an inside utility hosted in Azure App Service and also you wish to limit the entry solely along with your Group IP Handle or Community.
- Your utility shouldn’t be but dwell and also you wish to enable entry ONLY your inside group inside a spread of IP Addresses until your app goes dwell.
- You’re utilizing Deployment Slots and also you don’t wish to enable outdoors folks to entry the staging slots.
- You’re getting automated scraping requests from a set of IP Addresses and also you wish to block them.
- You wish to block web entry however you wish to Enable solely azure providers like Azure Utility Gateway or Azure Entrance Service
- Your app is an API that’s NOT meant to be accessed by public customers by solely consumed by trusted events.
On this article, we are going to discover ways to limit or enable entry to the Azure App Service utilizing the Azure Administration Portal.
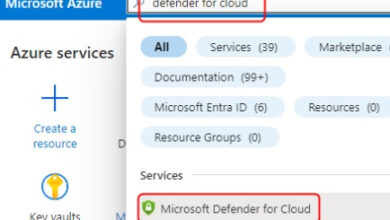
Azure Administration Portal
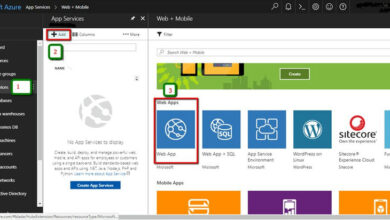
Let’s begin by navigating to the App Service (or a Staging Slot) and click on on Configure Entry Restrictions hyperlink which is obtainable within the Networking Blade as proven under.
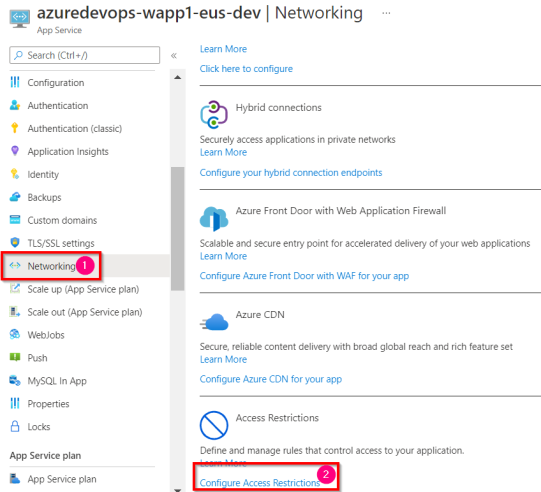
You’ll be taken to the Entry Restrictions blade as proven under.
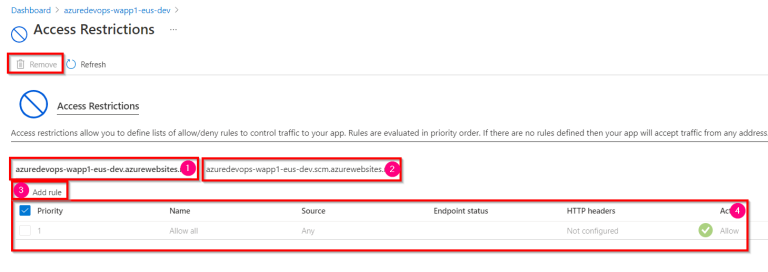
Under are the parts of the Entry Restrictions blade highlighted within the above screenshot.
- The primary tab reveals all of the entry restrictions utilized the Azure app service.
- The Second tab reveals all of the entry restrictions which are utilized for the Kudu web site. You’ll be able to be taught extra about Kudu right here.
- Add Rule button can be utilized create a brand new rule to be utilized for the entry restrictions of the app service.
- And at last you possibly can view all the present entry restrictions which are out there for the present app service.
Let’s now add new entry restriction rule on the app service by clicking on the Add Rule button.
Within the Add Entry Restriction blade, you possibly can present the next values to create a brand new Enable/Deny rule.
| Parameter | Description |
| Identify | The identify of the rule. |
| Motion | Enable – deciding on this selection will let the person entry the App Service from the given IP Handle (within the IP Handle Block) Deny – deciding on this selection will NOT let the person entry the App Service from the given IP Handle (within the IP Handle Block) |
| Precedence | The precedence given for this rule. |
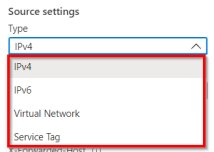
| Sort | Choose IPV4 (extra on this under) |
| IP Handle Block | Present the IP Handle Vary. If you need to say just one IP Handle then present one thing on this format 1.1.1.1/32 |
Observe
This text focuses on the sort IPV4. The method for IPv6 can also be the identical. Nonetheless, the Entry Restrictions function permits us to manage the entry utilizing the under varieties.
You’ll be able to go away the remainder of the fields as they don’t seem to be necessary and click on on the Add Rule button so as to add the rule. As soon as the rule is added. You discover the under two adjustments.
- The brand new rule with the values that you’ve got supplied will probably be added.
- The present Enable All rule with Precedence 1 will probably be turned into Deny Rule with a precedence 2147483647
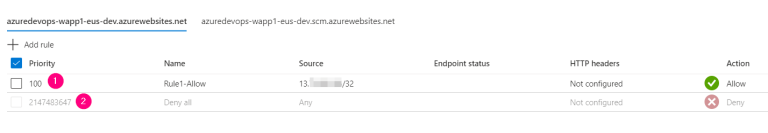
When you add a brand new rule (both Enable or Deny) a Deny All rule (proven within the above display) will probably be created and nobody will probably be allowed to entry the rule besides the Enable guidelines ones that are allowed explicitly utilizing the Entry Restriction blade.
That’s it. Now we have added an Enable rule for a Single IP Handle to entry the Azure App Service. Customers from different IP Addresses will be unable to entry the Azure App Service. In the event that they attempt to entry then they’d obtain an error with the message “Error 403 Forbidden – The online app your have tried to succeed in has blocked your entry” as proven under.
On this article, we have now realized the best way to manually enable/deny entry to a single IP Handle utilizing the Azure Administration Portal. Within the subsequent article, we are going to discover ways to carry out Bulk insertion of the IP Addresses utilizing PowerShell.
Hope it helps. Comfortable studying.