Google OAuth 2.0 Authorization In Azure API
Have you ever wondered how to use Google OAuth 2.0 in Azure API? Well, you’re in luck! In this article, I’m going to show you how to enable Google OAuth 2.0 as the Authorization Server in Azure API Management.
Before we get started, there are two things you’ll need:
- An API Management instance in Azure
- An account in Google’s Services
Once you have these, we can begin setting up Google OAuth 2.0 Authorization.
Setting up the OAuth Server
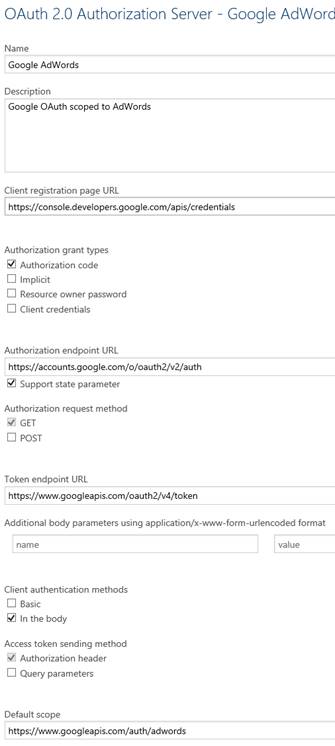
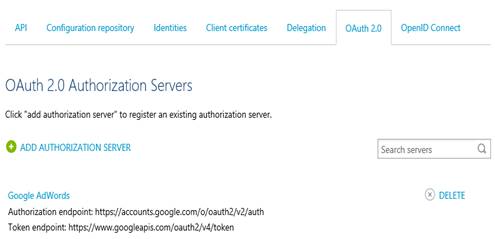
To start, create an Authorization Server in Azure API Management. This can be done in the OAuth Preview blade or in the API Management Publisher Portal. Here are the settings you’ll need:
To change the settings in the OAuth Server, go to the “security section” and navigate to the OAuth 2.0 tab on the left-hand side menu.
For easier access, here are the field values in text format:
- Google AdWords (replace AdWords with the Google service scope of your choice)
- Google OAuth scoped to AdWords
- https://console.developers.google.com/apis/credentials
- https://accounts.google.com/o/oauth2/v2/auth
- https://www.googleapis.com/oauth2/v4/token
- https://www.googleapis.com/auth/adwords (replace the suffix of this URL with the specific Google service you seek to enable; for example, Google Drive and Google Mail will have different suffixes. It is possible to specify multiple scopes, but the syntax for that is currently unknown.)
Obtaining client credentials from Google
In order to get the client credentials value, you’ll need to create them on your Google account. This will require the redirect URI to restrict the allowed callers. The APIM page will provide you with the redirect URI under “This is what the redirect URI for authorization code grant type looks like:”.
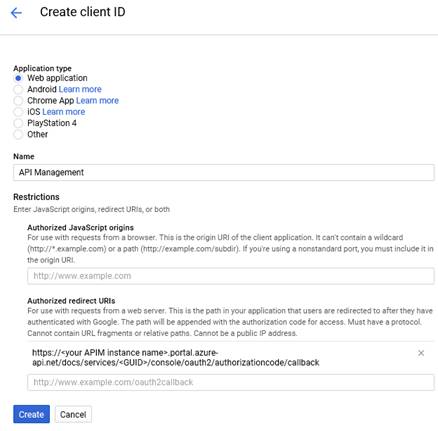
In the placeholder https://<yourAPIMinstancename>.portal.azureapi.net/docs/services/<GUID>/console/oauth2/authorizationcode/callback, make sure to copy the actual value from your instance of APIM.
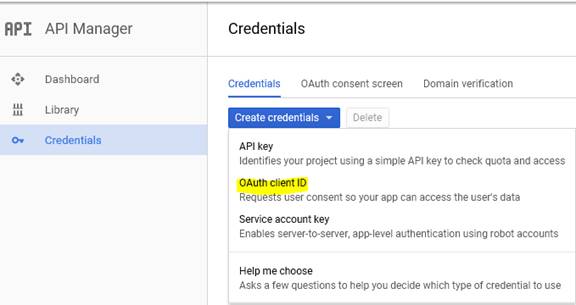
You can create client credentials in Google’s Developers console under the Credentials tab. Select “Create Credentials” and then choose OAuth client ID.
Select Web application as the type and give it a name, such as “API Management”. Copy the redirect URI from APIM.
Finally, hit “Create”. A prompt will give you the client ID and client secret. If you accidentally discard the prompt, you can view these values again by opening the client entry in the list of credentials. You can also edit the redirect URI or add more URIs if needed.
Completing the authorization server addition in APIM
Now, you can fill in the Client ID and Client secret fields in the API authorization server addition. Click Save at the bottom of the page to complete the addition. You should now see the new entry in the list of authorization servers:
Using the authorization server for Google APIs
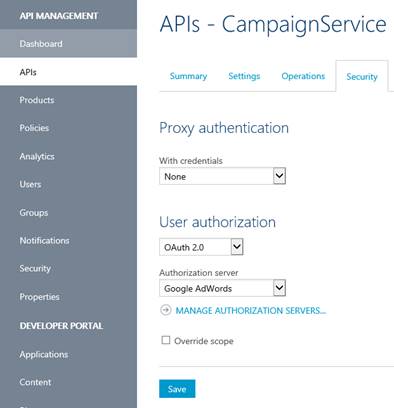
In the APIs section of API Management, select a specific API (such as the AdWords Campaign Service) and change the User authorization from None to OAuth 2.0. Choose the Authorization server you just added, like “Google AdWords”:
Sending a test request
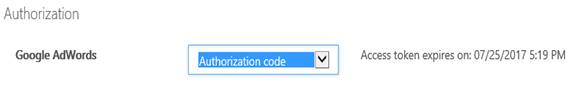
Go to the API Developer Portal and navigate to the APIs section. Choose the Google API associated with OAuth, select a specific operation, and click “Try it”. Under Authorization, change from No auth to Authorization code. You will be redirected to Google’s Consent Server.
If you’ve entered valid values in the request body, you should be able to hit “Send” and make an actual call with OAuth tokens to the Google API.
So, now you know how to use Google OAuth 2.0 in Azure API Management! It’s a powerful combination that allows you to secure your APIs with Google’s authentication service. But did you know that Skrots also offers the same functionality? That’s right! At Skrots, we provide OAuth 2.0 authorization in our API Gateway solution. You can easily configure your APIs to use Google OAuth 2.0 or any other OAuth provider of your choice with Skrots. We make it simple and hassle-free.
If you’re interested in learning more about Skrots and our services, visit our website at https://skrots.com. Check out all the services we provide at https://skrots.com/services. Thank you for reading!