Azure Storage CORS Ideas – CORS Guidelines Ideas – Half 5
When creating CORS guidelines for storage in Azure, it’s necessary to grasp what every rule will implement and what values are represented. Let’s take a better take a look at what CORS guidelines in Azure Storage seem like.
Please learn the earlier elements of the collection earlier than persevering with with this one,
- <Cors>
- <CorsRule>
- <AllowedOrigins></AllowedOrigins>
- <AllowedMethods></AllowedMethods>
- <AllowedHeaders></AllowedHeaders>
- <ExposedHeaders></ExposedHeaders>
- <MaxAgeInSeconds></MaxAgeInSeconds>
- </CorsRule>
- <CorsRule> … </CorsRule>
- <Cors>
That is the anatomy of a set of CORS guidelines in Azure. There are a number of issues which might be necessary right here. First, the illustration of CORS guidelines is XML, not JSON, or every other illustration. That is how Azure shops guidelines in uncooked type. As you will note in a number of the following demos, we’ll be working immediately with the XML illustration of guidelines. Some instruments will summary this XML illustration, but it surely’s nonetheless necessary to know what’s happening backstage, because it had been.
The second factor to level out is the basis CORS ingredient, it could possibly comprise zero or extra CORS rule components. Every CORS rule represents a single rule. The principles are evaluated by Azure in the identical order they seem on this format, so to reorder guidelines, you would want to control the present XML to reorder the CORS rule components. Let’s stroll by means of every of the rule properties in just a little extra element.
Allowed Origins
- <AllowedOrigins>
- https:
- </AllowedOrigins>
AllowedOrigins property is the way you’d specify the assorted allowed origin hostnames that may request sources. You possibly can both enter every origin individually utilizing a comma-delimited checklist, or you’ll be able to merely enter the wildcard to begin character to permit any origin. Additionally, be aware that Azure makes use of a case delicate actual match. There is no such thing as a wildcard prefix or suffix assist for this property. The origin should match precisely the origin that’s coming in.
Right here within the Azure portal, I’ve specified to solely enable the localhost area for CORS requests. Let’s check out what occurs in our earlier instance request from our localhost URL. The picture did not load as we’d anticipate.
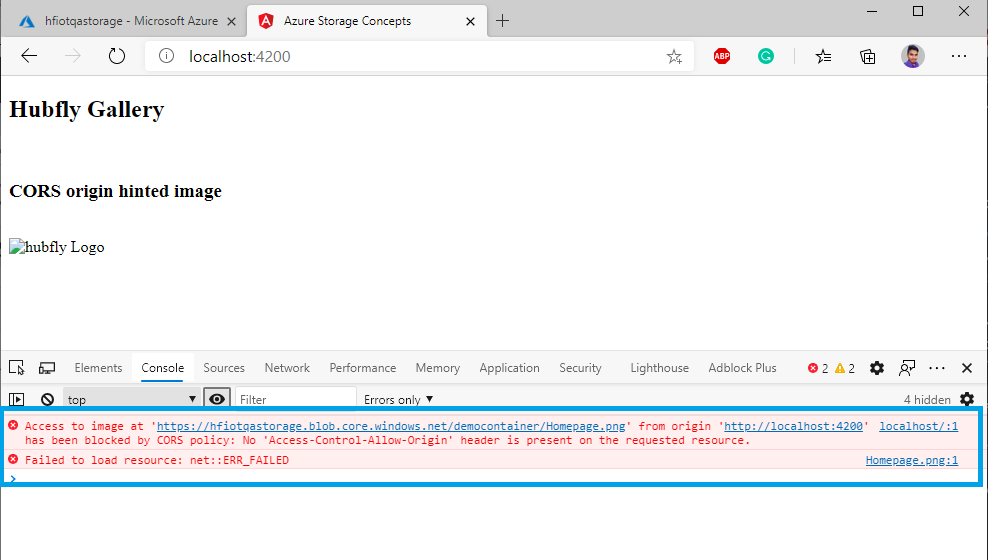
Let’s open the developer instruments and try the console. The error message right here says the entry management enable origin is lacking on the response. Beneath the origin didn’t match, the CORS rule evaluated failed and Azure will reply with the HTTP 403 forbidden response.
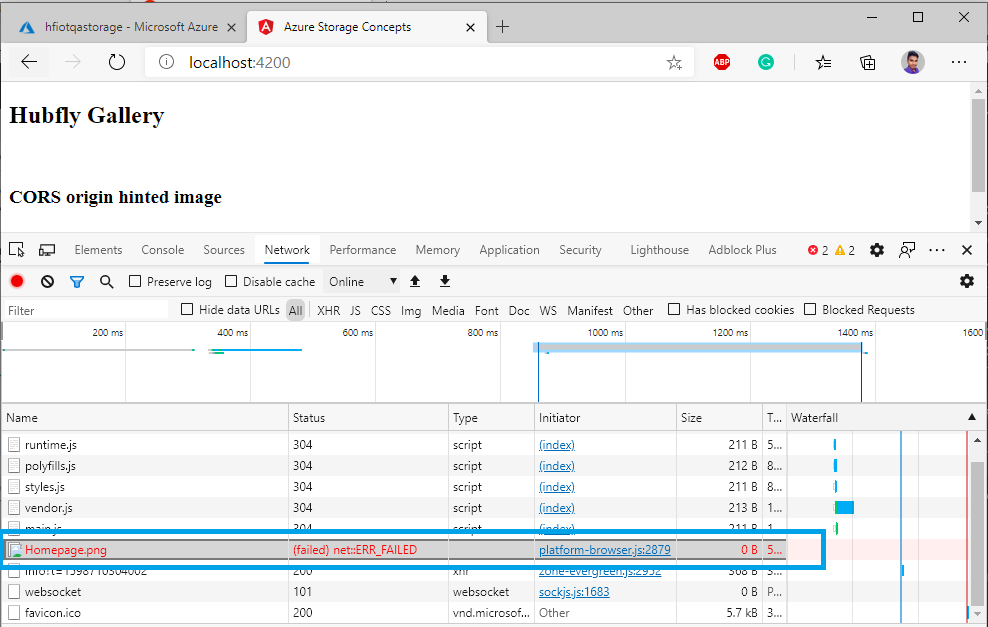
We are able to even take a peek on the Community tab if we refresh, we are able to see the request was canceled. Particularly, Azure did reply with an HTTP 403, however we are able to’t even see that as a result of the browser itself has canceled the request internally.
Allowed Strategies
- <AllowedMethods>
- HEAD, GET, OPTIONS
- </AllowedMethods>
AllowedMethods property restricts what HTTP verbs are allowed on request for sources. For instance, the rule solely permits the HEAD, GET, and OPTIONS strategies on a request. This could be a single or a number of worth checklist, separated with commas, and the checklist of strategies Azure helps DELETE, GET, HEAD, MERGE, POST, OPTIONS and PUT. Getting into a way not on the checklist just isn’t supported. Now, we recall the CORS pre-flight requests utilizing the OPTIONS technique. What would you anticipate to occur if we didn’t embody OPTIONS within the AllowedMethods checklist?
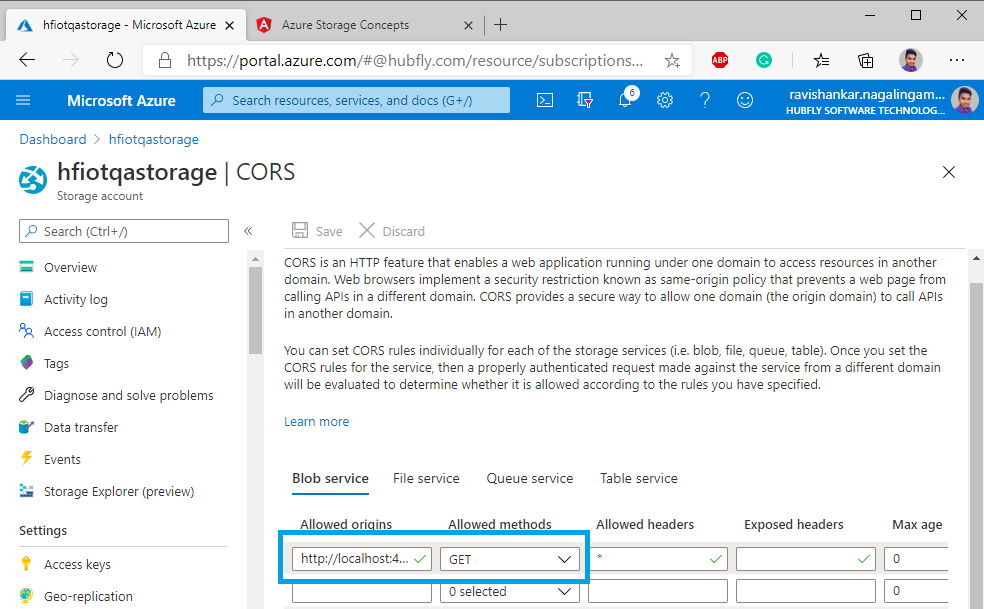
Effectively, let’s have a look. Again within the portal, I’ve now made positive I specify our localhost origin as an allowed origin, however now I’ve solely enabled GET requests.
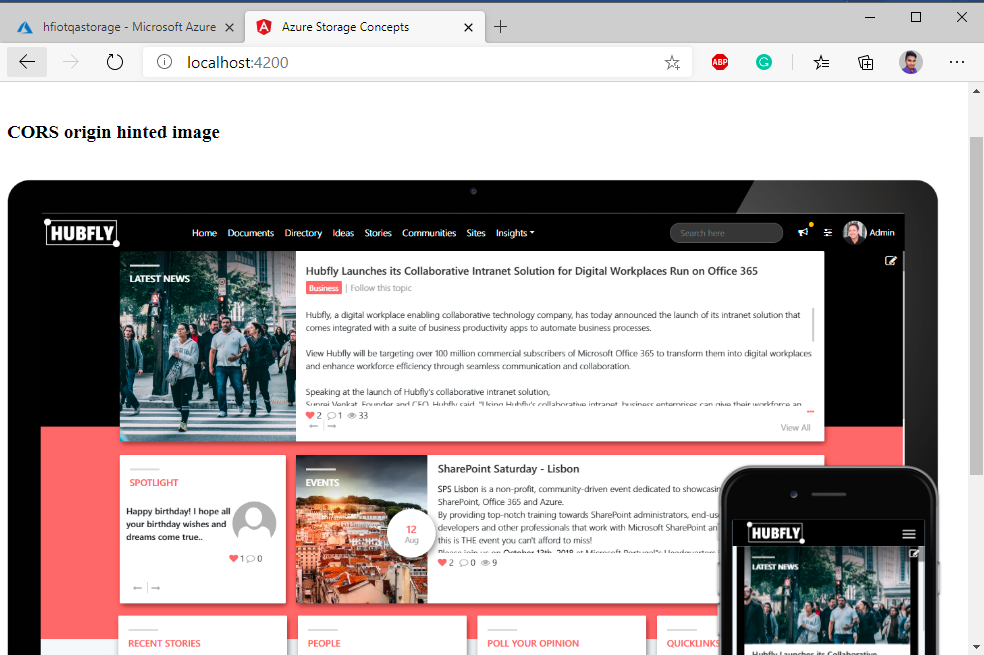
In our demo instance with a easy CORS picture request, we are able to see that the request has succeeded. Do not forget that this constitutes a easy request, so solely a GET was issued by the browser.
That’s it — I hope you have got discovered the right way to create CORS guidelines for Azure Storage utilizing AllowedOrigins and AllowedMethods properties. Within the subsequent article, we are going to see AllowedHeaders, ExposedHeaders, and MaxAgeInSeconds properties. Be at liberty to replenish the remark field beneath when you want any additional help.
