Deploy Packet Seize for Azure VPN Gateway
Introduction
We are able to seize the Azure VPN connection’s community packets utilizing VPN Gateway Packet Seize. We are able to choose the a number of tunnel community packets utilizing this VPN Gateway Packet Seize.
The packet seize knowledge recordsdata are generated in PCAP format.
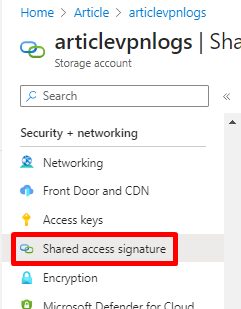
The Azure VPN Gateway packet seize requires the Azure Storage account, and we should create the SAS token to retailer the PCAP file.
In our earlier article, we discovered learn how to configure the Packet seize for the precise Digital Machine’s community site visitors utilizing Community Watcher.
This text teaches us learn how to seize the Azure VPN gateway’s site visitors utilizing VPN Gateway Packet Seize.
Step 1. Create a Container within the Storage account, open the container, and click on Shared Entry Signature (SAS) beneath the Safety + networking.
Step 2. Choose Blob beneath the Allowed companies, Choose Container beneath the Allowed useful resource varieties, and click on Generate SAS and connection string.
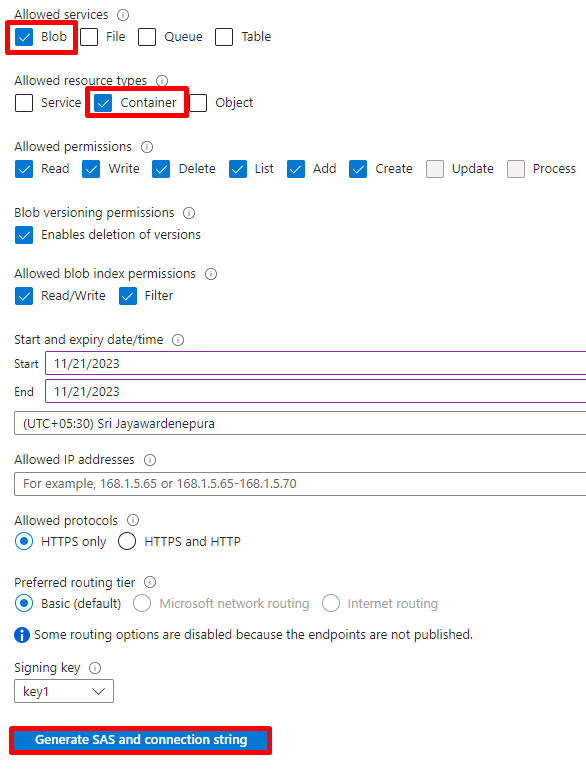
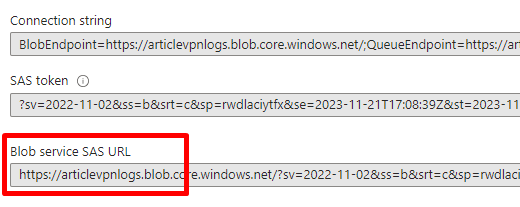
Step 3. Copy the Blob service SAS URL.
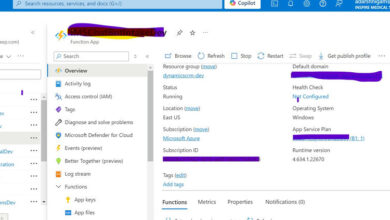
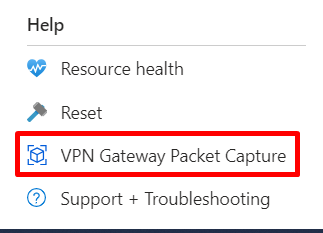
Step 4. Click on the VPN Gateway packet Seize beneath the Assist.
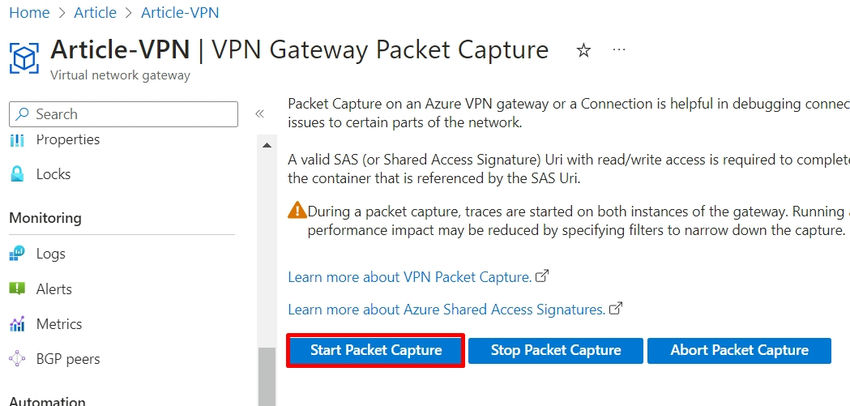
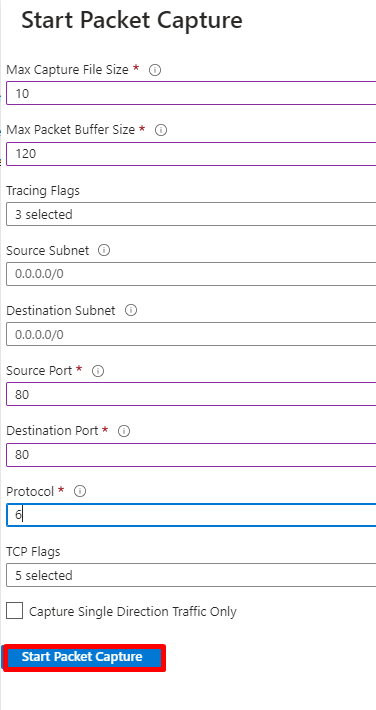
Step 5. Click on the Begin Packet Seize.
Step 6. The utmost Seize file measurement is 500M, so we will select the file Dimension.
The Max packet buffer measurement: The seize will solely include the contents of every packet truncated to this measurement.
We are able to specify the Supply Subnet and the Vacation spot Subnet.
We are able to set the Supply and the Vacation spot port.
As soon as the necessities are accomplished, you possibly can click on the Begin Packet Seize.
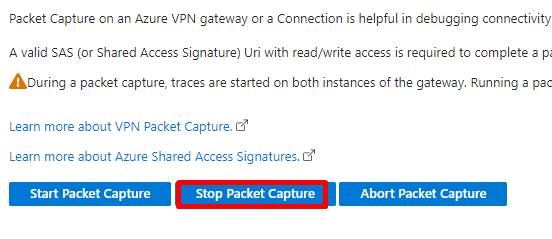
Step 7. Click on the Cease Packet Seize to cease the packet seize.
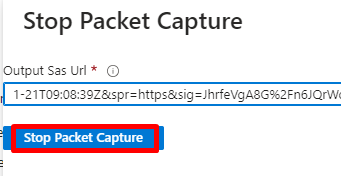
Step 8. Paste the SAS URL and click on Cease Packet Seize.
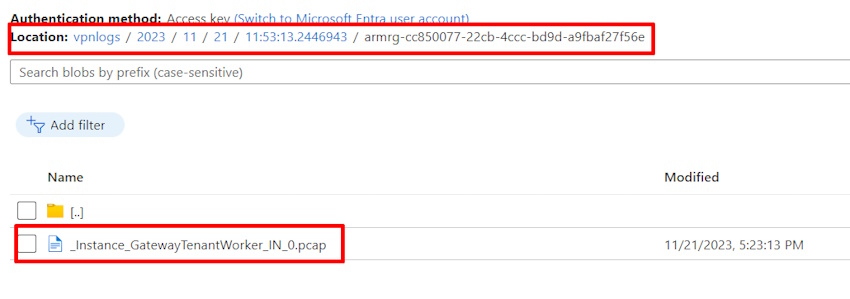
Step 9. Open the Container and obtain the pcap file to investigate the site visitors.
Abstract
This text taught us learn how to configure the VPN connection site visitors utilizing the Azure VPN Gateway packet seize. You probably have any questions, be happy to ask beneath the remark field.
Know extra about our firm at Skrots. Know extra about our companies at Skrots Companies, Additionally checkout all different blogs at Weblog at Skrots