The Enclave System Blueprint for confidential computing on the edge
A significant milestone in direction of making confidential computing in IoT mainstream for privateness and security.
In collaboration with Arm® Applied sciences and Scalys BV, we’re saying the rapid availability of the Enclave System Blueprint to assist in direction of making confidential computing a mainstream computing paradigm on the edge. The exponential progress in clever processing on the edge and autonomous command and management within the web of issues (IoT) necessitates confidential computing to guard privateness and security. Confidential computing on the edge calls for using security-hardened and tamper-resistant computing isolations known as Trusted Execution Environments (TEE) or just enclaves. Enclave units are extraordinarily complicated to engineer and function, and their absence is holding again the fullest potential in edge computing. The Enclave System Blueprint is right here to assist simplify the engineering of enclave units and deploying confidential purposes in IoT.
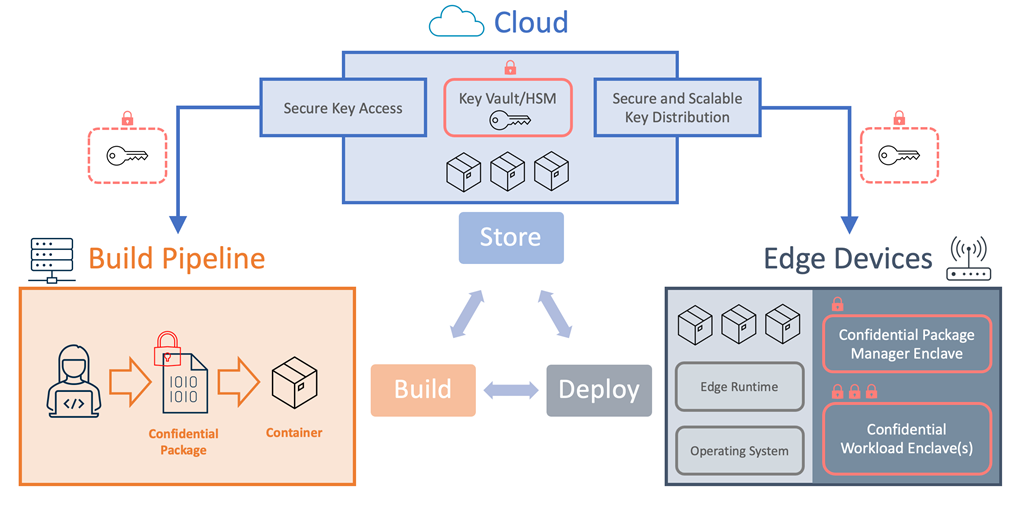
Determine 1: Enclave System Blueprint Structure
The rising want for confidential computing
Confidential computing augments conventional computing paradigms with further protections for computing workloads and knowledge when in use. Conventional computing applies cryptography to encrypt content material within the type of computing workloads, knowledge, and AI fashions when in storage or in transit however should decrypt mentioned content material in reminiscence when in use. This mannequin continues to work moderately effectively when working air-gapped compute networks the place there are decrease considerations for knowledge exfiltration or malicious tampering. IoT and cloud computing, however, ushers the age of computing characterised by hyperconnectivity, multitenant compute infrastructures, and data-driven autonomous command and management of many programs together with important infrastructure thereby calling for a better bar for privateness and security. Confidential computing utilizing TEE provides compute isolations needed to assist ship on each privateness and security to assist unleash the complete energy of digital transformations with IoT.
Particular issues for IoT
A significant distinction to look at in confidential computing within the cloud and on the edge is that whereas cloud resolution suppliers arrange and function the requisite infrastructure within the cloud for his or her clients, IoT resolution builders are accountable for developing with enclave units and the complexity in doing so holds them again.
As well as, whereas the infrastructure for confidential computing within the cloud resides in datacenters the place they profit from further facility and operational safety controls, IoT and enclave units are typically deemed to be beneath fixed menace of malicious bodily entry. To reduce this menace, enclave units are inclined to favor binding belief immediately or very near the basis of belief {hardware} (naked steel) over using supervisory software program like hypervisors and container runtimes to maintain the Trusted Computing Base (TCB) at a minimal. Supervisory software program however assist summary from the {hardware} to allow scale throughout {hardware} applied sciences at a price of a bigger TCB. Having to keep away from the size benefits of supervisory software program for greater safety is one supply of complexity in constructing, working, and sustaining enclave units.
The Enclave System Blueprint at its core seeks to resolve these challenges in a way that also upholds safety on the highest ranges potential.
The Enclave System Blueprint
The Enclave System Blueprint contains initiatives, assets, and steering to summary and simplify the event of enclave units and facilitate the deployment of confidential purposes at scale for IoT. It strives to enrich conventional computing by filling within the architectural and element gaps in direction of making confidential computing mainstream in IoT.
The blueprint is agnostic of {hardware} applied sciences, working programs, or resolution cloud. It invitations a group method to resolve a really complicated drawback the place individuals can mitigate value by collaboration and foster greater safety by the transparency that comes with open supply. All blueprint parts are at the moment in open supply and had been developed with the imaginative and prescient for full group possession and governance.
An actual-world realization
Greater than only a assortment of initiatives, assets, and steering, we made certain to validate the efficacy of the Enclave System Blueprint with a real-world machine and venture. The Enclave System Blueprint was impressed by the true statement of the roadblocks holding again confidential computing on the edge. It was, subsequently, necessary to make sure the blueprint tackle obstacles from actual experiences and is backed by actual product fact.
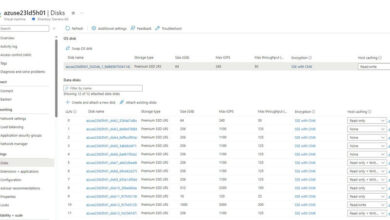
Whereas in collaboration for the event of the Enclave System Blueprint, Authentic System Producer (OEM) and secured units builder, Scalys BV, in tandem engineered TrustBox Edge 201 from the blueprint to fulfill each Azure IoT Edge licensed and tamper-resistant enclave machine necessities for confidential computing in IoT.
Determine 2: TrustBox Edge 201 (Supply: Scalys 2021)
Constructing on Azure cloud and making use of absolutely managed companies like Azure IoT Edge, Azure IoT Hub, Azure Capabilities, and Azure Key Vault, we included the software program parts of the Enclave System Blueprint to orchestrate an end-to-end at scale build-deploy pipeline for confidential purposes in IoT. It’s the modular nature of the Enclave System Blueprint parts that make it agnostic to know-how, working system, or the cloud. The total venture is accessible on Azure Samples and able to check out utilizing TrustBox Edge 201 from Scalys BV. The Enclave System Blueprint whitepaper offers an in depth clarification for the blueprint parts.
The journey continues
The Enclave System Blueprint delivers a serious milestone geared toward spurring the creation of enclave units and deploying confidential purposes at scale in IoT. Enclave units assist present privateness and security protections needed for IoT to unleash its fullest potential. Primarily based on historical past, one can safely assume that this is just one of many milestones, the obvious subsequent being seamless integrations with confidential computing companies within the cloud for uniform and pervasive cloud-edge confidential computing experiences.